Getty Photographs
A world solid of legislation enforcement businesses has struck a blow at a cybercrime linchpin that’s as obscure as it’s instrumental within the mass-infection of gadgets: so-called droppers, the sneaky software program that’s used to put in ransomware, adware, and all method of different malware.
Europol mentioned Wednesday it made 4 arrests, took down 100 servers, and seized 2,000 domains that have been facilitating six of the best-known droppers. Officers additionally added eight fugitives linked to the enterprises to Europe’s Most Wished checklist. The droppers named by Europol are IcedID, SystemBC, Pikabot, Smokeloader, Bumblebee, and Trickbot.
Droppers present two specialised features. First, they use encryption, code-obfuscation, and comparable strategies to cloak malicious code inside a packer or different type of container. These containers are then put into e-mail attachments, malicious web sites, or alongside reputable software program accessible by means of malicious internet adverts. Second, the malware droppers function specialised botnets that facilitate the set up of further malware.
In years previous, droppers have been distinctive to many alternative malware households. As evasion strategies have gotten tougher and the cybercrime panorama has grown evermore specialised, droppers have develop into stand-alone providers of their very own. A single unnamed suspect within the investigation has pocketed practically $75 million in cryptocurrency, Europol mentioned. Investigators are actually actively searching for methods to grab the digital funds.
By disrupting a half-dozen of essentially the most energetic droppers, legislation enforcement officers hope to sever the infrastructures which might be essential for the bigger malware and botnet ecosystem to thrive. Operation Endgame, the title Europol gave to the takedown effort, is the most important operation to ever goal botnets, the officers mentioned.
“Operation Endgame doesn’t finish immediately,” the officers mentioned. “New actions shall be introduced on the web site Operation Endgame.”
Beneath the operation, the officers have:
- Arrested 4 people (three in Ukraine and one in Armenia)
- Served 16 location searches (11 in Ukraine, three in Portugal, one in Armenia, and one within the Netherlands)
- Taken down or disrupted greater than 100 servers situated in Bulgaria, Canada, Germany, Lithuania, the Netherlands, Romania, Switzerland, the UK, the US, and Ukraine
- Seized greater than 2,000 domains
International locations collaborating in Operation Endgame embody Denmark, France, Germany, the Netherlands, the UK, and the US. Non-public companions included Bitdefender, Cryptolaemus, Sekoia, Shadowserver, Staff Cymru, Prodaft, Proofpoint, NFIR, Computest, Northwave, Fox-IT, HaveIBeenPwned, Spamhaus, DIVD, abuse.ch, and Zscaler.
Wednesday’s Europol discover acknowledged:
Europol facilitated the knowledge trade and offered analytical, crypto-tracing and forensic assist to the investigation. To assist the coordination of the operation, Europol organized greater than 50 coordination calls with all of the nations in addition to an operational dash at its headquarters.
Over 20 legislation enforcement officers from Denmark, France, Germany and the USA supported the coordination of the operational actions from the command publish at Europol and a whole bunch of different officers from the completely different nations concerned within the actions. As well as, a digital command publish allowed real-time coordination between the Armenian, French, Portuguese and Ukrainian officers deployed on the spot through the area actions.
The command publish at Europol facilitated the trade of intelligence on seized servers, suspects and the switch of seized knowledge. Native command posts have been additionally arrange in Germany, the Netherlands, Portugal, the USA and Ukraine. Eurojust supported the motion by establishing a coordination heart at its headquarters to facilitate the judicial cooperation between all authorities concerned. Eurojust additionally assisted with the execution of European Arrest Warrants and European Investigation Orders.
The officers additionally added the names, footage, and descriptions of eight males to Europol’s most wished checklist:
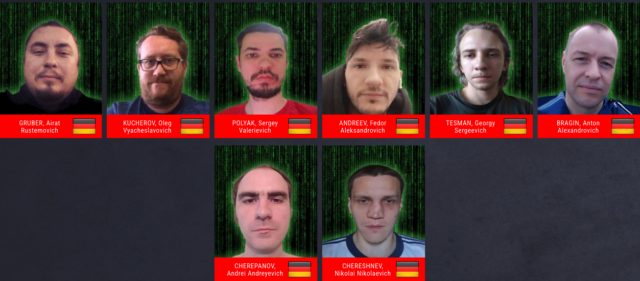
Europol
The officers additional introduced operation-endgame.com, a website devoted to the continued crackdown on droppers. It adopts a lot of the identical swagger and smack speak ransomware name-and-shame websites direct at victims and targets. FBI officers equally trolled members of the LockBit ransomware syndicate in February once they arrange a website following a separate disruption operation.
“Worldwide legislation enforcement and companions have joined forces,” Operation Endgame investigators wrote. “We’ve got been investigating you and your felony undertakings for a very long time and we is not going to cease right here.”